In a moment we’ll share a security update from OZnzb in response to the Heartbleed bug. Whether you are a member of OZnzb or other indexers I agree with their recommendation of updating your credentials. Especially if you share passwords between sites. Heartbleed hit over half the worlds websites. Usenet providers NNTP servers are safe from Heartbleed but your indexer may very well be affected. Ask them if you are unsure.
Here is the Heartbleed update OZnzb shared earlier this morning:
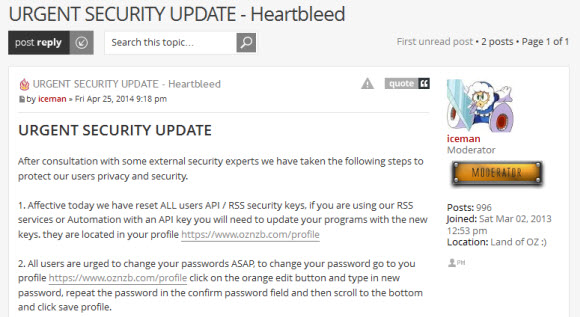
URGENT SECURITY UPDATE
After consultation with some external security experts we have taken the following steps to protect our users privacy and security.
1. Affective today we have reset ALL users API / RSS security keys, if you are using our RSS services or Automation with an API key you will need to update your programs with the new keys. they are located in your profile https://www.oznzb.com/profile
2. All users are urged to change your passwords ASAP, to change your password go to you profile https://www.oznzb.com/profile click on the orange edit button and type in new password, repeat the password in the confirm password field and then scroll to the bottom and click save profile.
If you have accounts on other indexers then we would strongly recommend that you also reset these credentials on those sites.
Our experts have confirmed that any site that was vulnerable to the Heartbleed SSL bug (which most indexers were and 60% of the worlds websites), anyone who had exploited this bug could have access to your accounts.
We apologise for any inconvenience this may cause you, however we believe this is a necessary step in protecting our users.
More information about the Heartbleed bug
Heartbleed is not a virus, but rather a mistake written into OpenSSL— open-source software for SSL implementation across the Web. It is a security vulnerability in OpenSSL software that may affect nearly two-thirds of websites online and allow hackers to access data servers that may contain username, password and other sensitive information.
With the disclosure of a bug in OpenSSL’s implementation of heartbeat, it is no longer necessary for cybercriminals to hack into the server to steal the credentials or private keys. An easy execution of a small code will provide them with wealth of information just by exploiting the vulnerability in OpenSSL. While this is happening, the server admin will never know that their server has been exploited and how much of the information has been leaked by the exploit.
Security researchers found out that an encryption technology SSL/TLS that helps in providing communication security and privacy over the network for various applications viz. web-based applications, email and VPN had this security flaw. This encryption technology that used to safely transmit e-commerce transactions, email, social networking data and other Internet traffic was affected by Heartbleed and this security flaw was enough for hackers to access user’s sensitive personal information.
This vulnerability allows anyone to steal the information which under normal circumstances is protected, by the SSL/TLS encryption. Therefore, attackers can steal a server’s digital key which is used to encrypt data and get easy access to an organization’s sensitive documents.
Security researchers also add that this newly discovered security vulnerability is extremely dangerous as it remained undiscovered for more than two years. However, Wolfgang Kandek, chief technology officer for Redwood City security company Qualys said that, it still remains unclear if hackers have taken advantage of the flaw to steal sensitive data from vulnerable sites.
Researchers at Codenomicon say that OpenSSL is used by two of the most widely used Web server software, Apache and nginx. This means a lot of internet sites would possibly have this vulnerability.
Kandek added, many affected websites will now have to have their encryption keys recertified as safe. That’s because even after fixing the flaw in their software, unsafe keys can easily allow hackers to steal sensitive personal information.
Moreover, every website / server / service admin, who uses OpenSSL should be concerned about this vulnerability as it breaks everything for which SSL encryption was deployed in the first place.



